Cyber Security
Security your Digital Frontier
In today’s interconnected world, cybersecurity is more critical than ever. AiPath leverages cutting-edge Data analytics driven intelligence to safeguard both IT and OT environments, ensuring comprehensive protection against evolving cyber threats. Whether you’re securing enterprise networks or industrial control systems, our AI-driven solutions provide real-time threat detection, response, and risk mitigation.

Security Types

Infrastructure Security
Reimagining the digital landscape, pioneering secure, innovative futures for businesses and cities globally.
Network Security
Elevating digital defenses with innovative network security, ensuring seamless and secure connections for a thriving digital ecosystem.
Advanced Endpoint Protection
Harnessing elite technologies for unmatched cyber resilience, protecting digital frontiers against tomorrow’s threats.
Email Security
Fortifying communication gateways, transforming them into bastions of inviolability with sophisticated email security protocols.
Zero Trust Security
Redefining security paradigms with Zero Trust frameworks, embedding perpetual vigilance into digital interactions for impervious networks.

Identity & Access Security
Shaping the future of security with cutting-edge solutions that safeguard identities, manage privileged access, and authenticate users.
Identity
Partnering with industry leaders, we deliver comprehensive Identity Governance and Administration, focusing on seamless management across identity lifecycles, access, policies, and analytics.
Privileged Access Management
Our PAM solutions fortify against insider threats, aligning privileged user management with strict security and governance standards.
Authentication
We ensure secure access through advanced authentication, protecting applications and accounts against unauthorized use.

Data Security
Empowering secure digital futures with advanced data protection, encryption and managed transfers, tailored to elevate enterprise security & compliance.
Data Protection
Crafting a secure future with our Data Protection Lifecycle, we ensure comprehensive coverage from discovery to compliance. Our approach safeguards data privacy, integrity, and prevents leaks, underpinned by expert consultancy and adherence to global standards.
Data Encryption
Specializing in both Symmetric and Asymmetric Encryption Technologies, we protect Data-at-Rest, Data-in-Transit, and Data-in-Use with bespoke solutions that meet your organizational needs, ensuring the highest levels of security.
Managed File Transfer
Our secure, centralized solutions automate and simplify data movements for enterprises, enhancing efficiency and safety across all operations.

Managed Security Services (SOC+)
Enhancing cybersecurity through continuous monitoring, proactive threat management, and strategic leadership for comprehensive digital protection.
Managed SOC and Analyst Services
Continuous monitoring, threat detection, and expert SOC analyst support enhance your security posture.
Proactive Threat Management
Utilizing threat intelligence, UEBA, and NBAD/NTA for early detection and mitigation of emerging threats.
Comprehensive Vulnerability and Endpoint Protection
Identifying vulnerabilities and rapidly responding to endpoint threats ensure system integrity.
Incident Handling and Forensics
Streamlined incident response, from automation to in-depth forensics, ensures quick and effective resolution.
Strategic Security Leadership
Offering vCISO services for expert guidance and strategic direction in cybersecurity efforts.
Technology Partners
















Security Types

Asset Monitoring: Comprehensive Asset Management and Threat Detection
Stay in control with Asset Monitoring, providing:
Asset Discovery & Intelligence
Identify and track your assets.
Threat Intelligence
Stay ahead of potential threats.
Asset Behavior Analysis
Detect anomalies in asset behavior.
Cyberthreat and Vulnerabilities
Identify and mitigate risks.
Risk & Anomalies
Monitor for security risks and anomalies.
Security Visibility
Gain comprehensive security insights.
Intrusion Detection
Detect and respond to intrusions effectively.
Centralized Management
Efficiently manage assets.

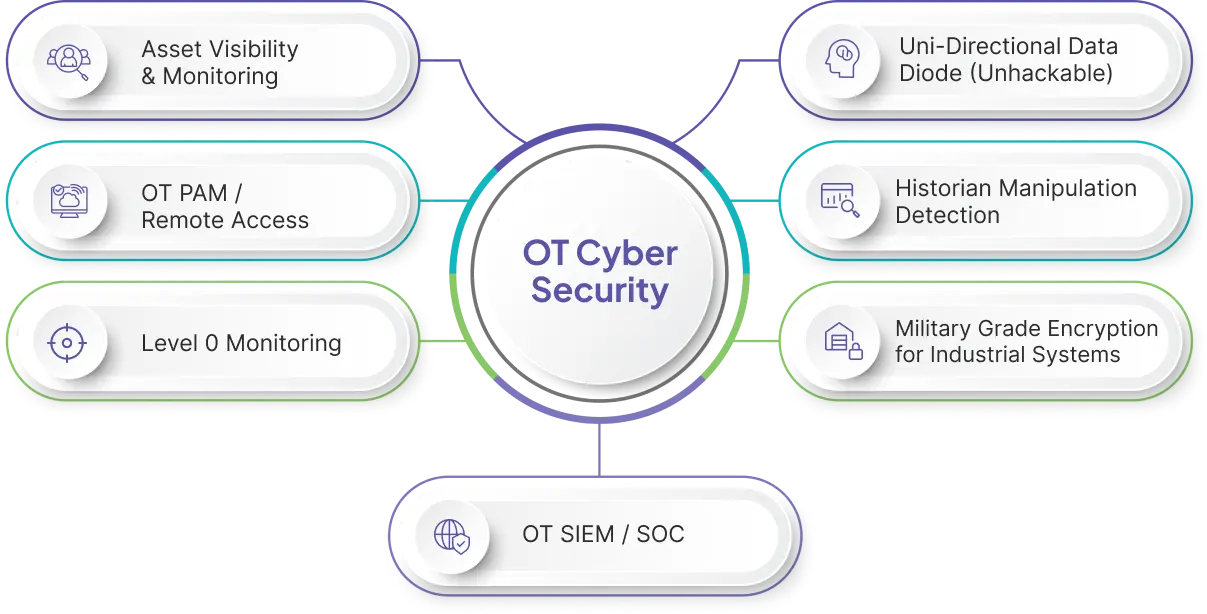
IT/OT Cybersecurity: Secure your OT Environment
Our IT/OT Cybersecurity solution ensures:
Privileged Interactive Access
Manage privileged access securely.
Threat Intelligence
Stay ahead of potential threats.
Asset, Patch & Configuration Monitoring
Monitor asset status, patches, and configurations.
Logging & Situational Awareness
Maintain detailed logs and situational awareness.
Endpoint Password Management
Secure endpoint passwords.
Patch Gap Analysis
Identify gaps in patch management.
Compliance Reporting
Generate compliance reports.
Incident Response Ticketing
Streamline incident response.
Workflow Compliance
Ensure compliance with workflows.
Root Cause Reports
Analyze and address root causes.
Serial Level Access
Secure serial-level access.
Designed for OT
Tailored for OT environments.

Level Zero Monitoring: Enhance Visibility and Predictive Analysis
Gain a deeper understanding of your OT infrastructure with Level Zero Monitoring. Our solution provides:
Comprehensive Visibility
See every aspect of your infrastructure.
Predictive Analysis
Anticipate issues before they occur.
Predictive Maintenance
Keep your assets in optimal condition.
Asset Performance Optimization
Maximize asset efficiency.
Level Zero Cyberattacks
Defend against threats at the foundation.
Regulatory Reporting
Simplify compliance.
Electrical Efficiency
Optimize energy usage.
Safety Management
Enhance operational safety.
Local Dashboard
Access localized control and monitoring.

Encryption for Low Computing Devices: Secure Encryption for Resource-Constrained Devices
Our solution includes:
Encryption for Low Computing Devices
Secure low-power devices.
Video Encryption
Safeguard historian data.
TLS 1.3 Support
Utilize TLS 1.3 for secure communication.
30 Times Faster
High-speed encryption.
Synchronized Algos
Utilize synchronized algorithms.
Key Exchange
Ensure secure key exchange.
Mitigate MiM and DDoS Attacks
Protect against MiM and DDoS attacks.

Perimeter Defense Solution: Robust Perimeter Security
Our solutions offer:
Unhackable
Network and Digital Asset Security.
Historian Replication
Safeguard historian data.
Log Forwarding
Forward logs for analysis.
Screen Replication
Secure screen replication.
OPC Replication
Protect OPC communications.
Bidirectional Protocol Support
Support bidirectional protocols.
Secure Patching for ICS
Apply patches securely.
Span Mirroring
Implement effective span mirroring.

Data Forgery, Manipulation & Sensor Fault Detection: Advanced Data Protection and Anomaly Detection
Our solution provides:
Connect to Any Data Source
Access data from various sources.
Unsupervised Machine Learning
Utilize machine learning for detection.
Reliable Detection Engine
Detect anomalies and manipulation reliably.
Extensive Dashboard
Access a comprehensive monitoring dashboard.
Real-time Alerts
Receive alerts in real time.
Notifications
Stay informed of critical events.
Root Cause Analysis
Investigate and address root causes effectively.
Invisible Network: Secure Communication and Policy Enforcement
Invisible Networks ensure secure communication and policy enforcement:
Bidirectional Communications
Enable secure two-way communication.
End-to-End Encryption
Protect assets with encryption and MFA.
Asset Mobility
Ensure policies follow assets, regardless of location.
Policy Simplification
Simplify policy creation and enforcement.
Layer 3 Switching
Implement advanced networking capabilities.
Air Span Mirroring
Monitor air span effectively.
Technology Partners













Let's Transform Your Business
Take the next step in your digital transformation with us, We have the expertise to make your vision a reality.
